Customer Relationship Management (CRM)
Data Farm
Inc.®
|
The Technical "Know-How"
|
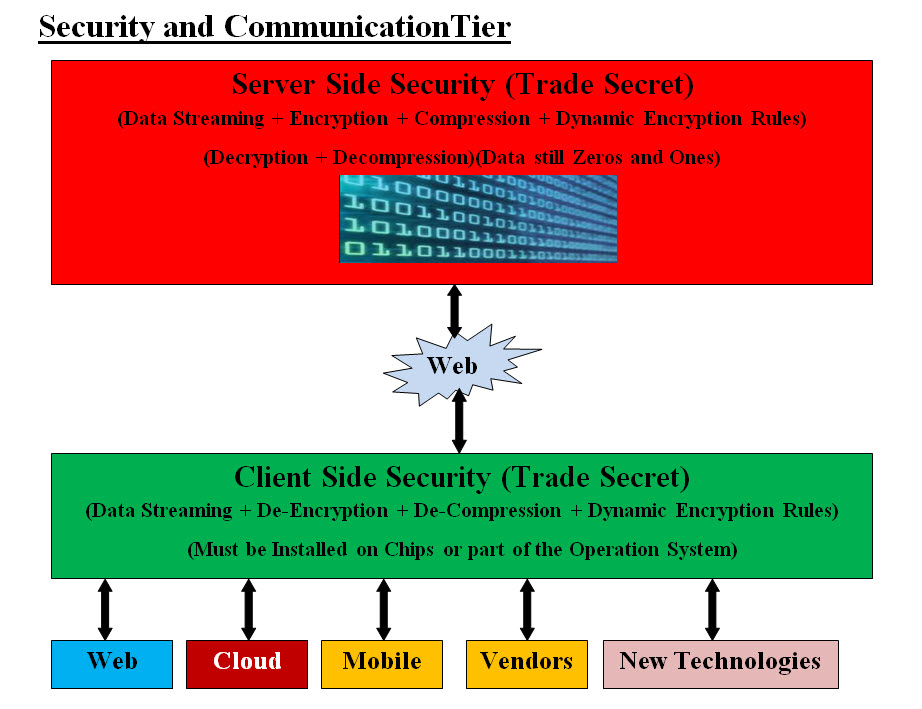
Security and Communication Tier - Too Good to Be True
Sadly, security is never ending battle, plus hackers are becoming more
sophisticated and have the latest tools. Not to mention, employees may
possibly be part of the hackers' teams.
Our answer to both internal and
external security is done by combing data compression and encryption
to create a new compressed-encrypted data that is less than 35% of its
original size, dynamically encrypted and has no value to the anyone unless
they unlocked what we did. The keyword "Dynamically" means the locking-unlocking
mechanisms have an infinite number of encryption keys for each IP address which
our security would be communicating with. Again, zeros and ones are our infinite
number of encryption keys. This is too good to be true and luckily for us
it is true. The following image presents a rough picture of our Security and Communication Tier.
|
|