Customer Relationship Management (CRM)
Data Farm
Inc.®
|
The Technical "Know-How"
|
Investors
Our Entrepreneurial Two Cents Worth for Investors
• What are the Main Issues?
• What Problem We are Aiming To Solve?
• Investors FAQ
• Our Security System
• How can we go about building our Post Office?
What are the Main Issues?
Let us look at the top three.
#1: Cyber Security Market
According to the Forbes magazine, cyber security is expected to reach $170 Billion by 2020.

#2: Big Data:
The challenges that businesses face is making use of data that is growing at an exponential rate.
#3: Cloud, Mobile and Database:
Wireless data (signals) is an open invitation for the taking, and cloud is the same
where data is being transmitted between hosts and service providers. Databases are
target practice for internal and external hackers and employees.
What Problem We are Aiming To Solve?
We are building a Data Farm in the cloud plus the mobile part of it.
Our CRM Data Farm (our Post Office Project) would handle Security,
CRM, Big Data, Business Intelligence (BI), Analytics, Intelligent
System, Data Stream, Governance and end-to-end solution.
Investors FAQ
What are our investors investing in?
Our Post Office project is composed of the following subsystems or services:
• Security using Compression-Encryption
• Data Services
• Intelligent Data Analysis
Each can be sold separately or combined with other services, and can be easily integrated
with any existing system. We believe our best seller is Security using Compression-Encryption. The
question is "Why". It will put hackers (internal and external) out of business and will change how
to build security. Our conceptual model would leave unauthorized infringers puzzled and unable
to access our compressed encrypted data.
What is the goal of our Post Office project and how can it be achieved?
Our Post Office Project's architecture is based on the following concepts and approaches:
|
1.
|
Compression: compressing or zipping data to a smaller size
|
|
2.
|
Encryption: making data have no value to unauthorized infringers
|
|
3.
|
Intelligence: software system with a Brain that thinks in abstract and is self correcting
|
|
4.
|
Intelligent Data Access Object (IDAO): making data intelligent and not a dummy storage place
|
|
5.
|
Indexing: converting values to numbers for faster processing
|
|
6.
|
Hashing: converting data to smaller values (not necessarily numbers) for faster processing
|
|
7.
|
Mapping: converting data to different formats for faster and easier processing
|
|
8.
|
Dynamic Business Rules: dynamically mapping the business processes
|
|
9.
|
Speed-Performance-Refactoring: optimizing performance, processing, services, data handling, development and refactoring
|
The following matrix outlines which approach strategy and processes would be paired with each service.
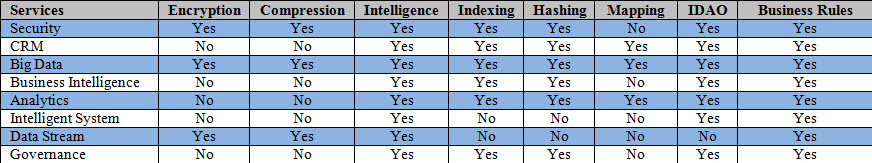
Our Dynamic Business Rules is the key in making system changes without modifying any code or processes.
Our Security System
Our Security System uses algorithms which can compress files or data (Lossless) to
more than 65% of its original size. Lossless compression is a class of data compression
algorithms that allows the original data to be perfectly reconstructed from the compressed
data. Our algorithms run as fast as CPU speed and we can also create a security chip
with its own CPU, memory and Math Coprocessor for faster performance. Each chip would
have its own unique IP Key that maps each client's IP address/Mobile ID into an internal
storage cell/register. The IP Key is used in compression-decompression-encryption-decryption
code. The IP Key can also be dynamically loaded and changed for adding an additional level of security.
Our Security Gatekeeper
Our Security Gatekeeper can be a chip or software which receives only certain types of signals
or files which has the client's IP address. Our Security Gatekeeper will identify the incoming
data or signals and check for authentication and authorization. It would perform
compression-decompression- encryption-decryption code on these files or signals. Our Gatekeeper
can be turned On/Off and the connection would return back to the client's original security setting.
What will our Compression-Encryption replace?
• Secure Sockets Layer (SSL)
• Hypertext Transfer Protocol Secure ( HTTPS)
• Firewall
• Any security software
How can we go about building our Post Office?
|
•
|
We can use CRM Data Farm Inc. and market our products which will be timely and costly.
|
|
•
|
Buy an existing data vendor and integrate our services with its services.
|
|
•
|
Build a company and compete with big data vendors in hopes of a highly profitable acquisition.
|
|
•
|
Get one of the big data vendors to invest in our Post Office project and run as a daughter company through their name and credibility.
|
|
|